The recent rush from SASE to SSE
By Martin Vilaboy
It’s not uncommon for things to move quickly within the realm of business IT and networking technologies. And the rate of innovation and service displacement only has accelerated. But the time it took SSE to challenge SASE must be some kind of record breaker. Before SASE could even approach its overinflated peak of hype as the next hot networking framework, contestants were making the case of “Why SSE is the new SASE.”
Much of this debate comes down to the difference an ‘A’ makes in secure access service edge (SASE) and secure service edge (SSE), two terms both coined by Gartner in 2019 and 2021, respectively. Both SASE and SSE aim to enable the transition of corporate networks away from serving and defending resources behind a fixed network perimeter to serving and defending any application, user or resource no matter where it resides, with users and devices treated with equal suspicion, explain editors at CyberRisk Alliance, precisely what IT leaders need at a time when remote work is expanding the attack surface, while the use of cloud applications and edge resources are exploding. Neither acronym represents any “new” technology but rather a conglomeration of technologies brought together to support the goal of integrated networking, access control and security.
In terms of separating the two, SASE describes an architectural framework that consolidates networking – typically SD-WAN – and the security stack – typically cloud access security broker (CASB), secure web gateway (SWG) and zero trust network access (ZTNA) – delivered as a unified cloud-based service. SSE describes the security-as-a-service portion of this framework, leaving out the networking-as-a-service part, explained Mor Ahuvia, product marketing manager for cybersecurity provider Checkpoint.
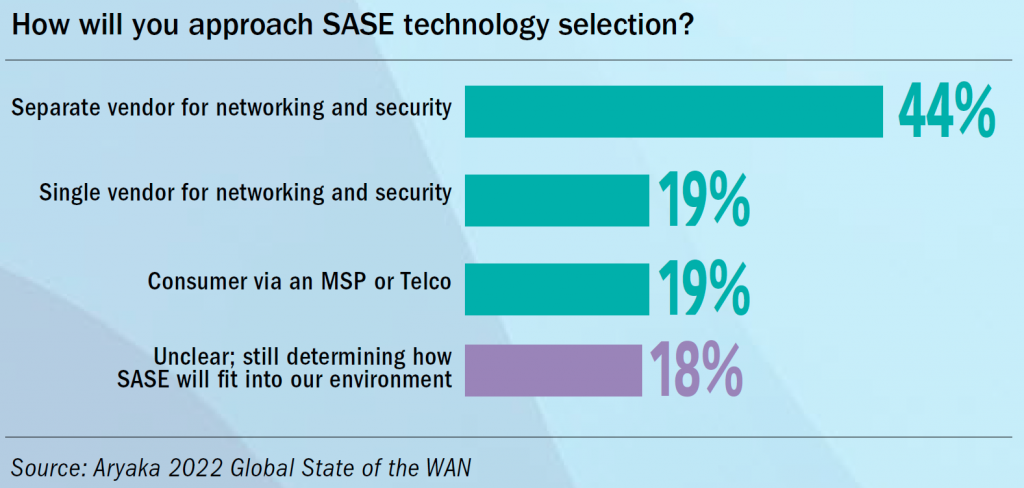
“This new acronym reflects the observation that while organizations are looking to consolidate and simplify their network security for remote and hybrid workers, some prefer a best-of-breed, dual-vendor approach with separate solutions for networking-as-service and security-as-a-service,” Ahuvia continued.
In other words, some have described SSE as effectively SASE without the SD-WAN, or the “access” element. The market and marketing have become quite crowded and confusing because contestants have entered the SASE space from a range of sectors including enterprise networking, enterprise security, cloud security, endpoint security, content delivery, wide area network (WAN) management and acceleration, telecom and managed services.
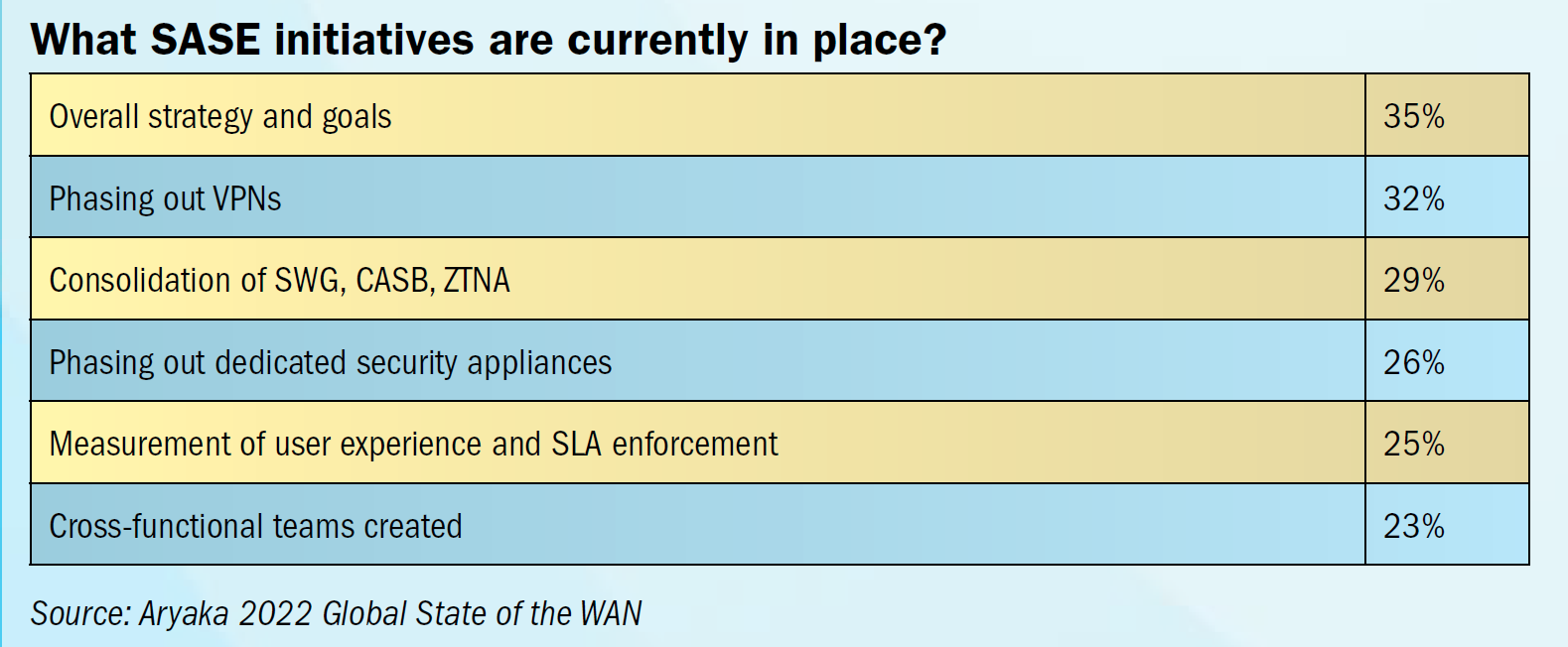
Indeed, SASE entails a lot of moving parts, representing the convergence of software-defined network and network access, identity service brokering and several formerly disparate security functions into one cloud-delivered framework.
“The future vision of all SASE architecture is to deliver the joined networking and security functionality in an as-a-service model,” explained Yuval Yatskan, senior director of solutions and product marketing for SASE at Cisco.
“Because SASE architecture combines both networking and security functionality, a full SASE approach requires a coordinated and cohesive approach across both network security and networking teams,” Yatskan continued.
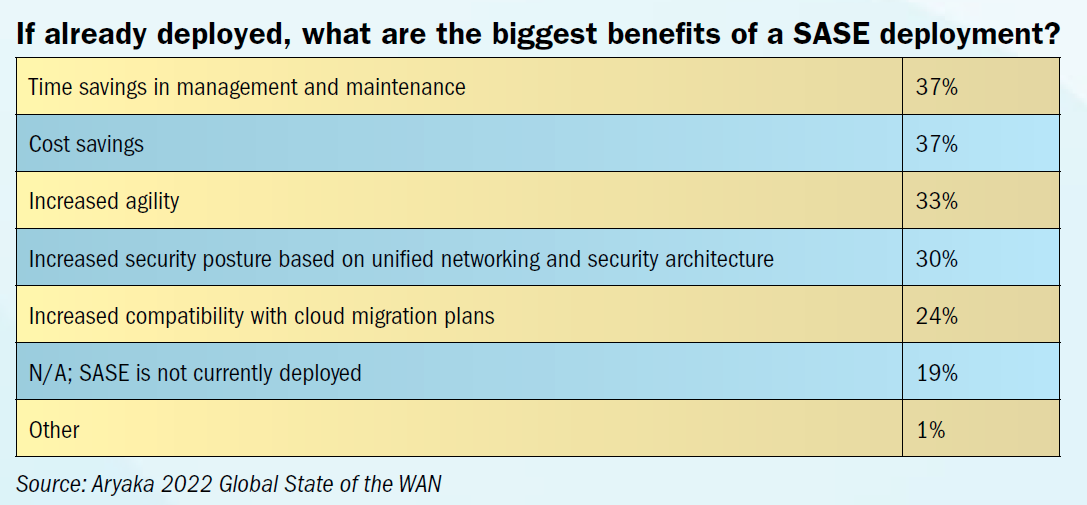
All the while, many larger organizations still operate with independent networking and security teams, and still prefer this consumption model. Many also still prefer a best-of-breed, dual- or multi-vendor approach with separate solutions for networking-as-service and security-as-a-service. Due to the sheer complexity of SASE, as well as the potential distance between investment cycles within networking and security departments, many enterprises simply may find it more practical to implement SASE in stages, argued CyberRisk Alliance analysts. So perhaps it’s not surprising that it is taking some time for SASE offerings and adoption to mature. Despite the hype, for instance, there are very few vendors currently offering a fully unified and comprehensive SASE solution.
There’s also the COVID 19 factor. Lockdowns meant corporate resources had to be extended out to kitchen tables and coffee shop Wi-Fi; cloud services adoption rapidly accelerated. Gartner’s shiny new SASE framework was right there on the edge, seemingly created for the circumstances. The prospect of a cloud-delivered combination of network (access) and security that could reach to and beyond the edge of networks suddenly became very enticing.
And with the shift to remote and hybrid working, one could argue that security was a more immediate and widespread problem than access. Even when access was only adequate or barely serviceable, at least the last mile connection already was in place for most knowledge workers. Security measures, on the other hand, largely were not; and the threats to sprawling networks were real and sometimes expensive to resolve.
The means of delivering the “access” in a SASE framework, meanwhile, typically SD-WAN, often makes sense for office locations, as well as branch and satellite offices, but delivering it to home tends to be cost prohibited outside of certain job functions and executive levels. And if an SD-WAN solution already is in place, an architecture composed of an SSE security suite that’s tightly integrated with a separate vendor’s SD-WAN, argued Gartner analyst Charlie Winckless, could perform as well, if not better, than a single-vendor SASE approach.
In many market segments, Winckless told SDxCentral, particularly large businesses, there is a preference toward standalone-security functionality, while proponents of SSE also argue that security stacks offered by companies specializing solely in SSE tend to be a step ahead of the security functions offered by SD-WAN providers that have developed a SASE framework.
‘A’ for All
Proponents of a unified SASE approach, on the other hand, would argue that any step toward uncoupling networking and security is a step in the wrong direction and defeats the core premise of an integrated, application-centric approach offering end to-end visibility and control.
While SSE offers some conveniences for enterprises, “it only reinforces the current status quo of a fragmented security market and doesn’t address new attack surfaces in the rapidly changing security landscape,” said Renuka Nadkarni, chief product officer at Aryaka.
SSE underestimates the complexity of traffic aggregation from multiple sources such as branch offices, remote and mobile users, said Nadkarni. “The biggest challenge and complexity here is the rapidly changing WAN/5G accessibility for guaranteed application (and network) performance and availability.”
It took years to come to a unified SASE architecture that brings together context from both the networking and security stacks, argued Cato Networks co-founder Gur Shatz. Segmenting a SASE architecture that’s divided up between the respective teams (networking or security) runs the risks of missing out on the shared context enabled by a singular approach, Shatz told SDxCentral, while adding confusion to the mix, as it can be unclear which team is responsible for what.
“Whenever you have two things making a decision independently, you have a security hole,” Shatz continued.
“SSE is a convenience for box vendors using a network-centric approach to move the finite capabilities of their box into the edge/cloud,” said Nadkarni. “It is not the modern application-first centric thinking, and hence it’s dead on arrival.”
The need to lockdown workforces when the lockdowns greatly expanded the attack surface certainly made SSE highly attractive for the better part of the last two years. And while the SSE market may have matured faster and in a more consolidated fashion, the ability to have complete control and visibility, as well as performance and reliability, out to the edge of networks will be a competitive advantage, if not a strategic necessity, in the long term. That could require an infrastructure in which networking and the security stack share context across a single control plane, thus minimizing “gaps” between the two.
So rather than being a “replacement” or “alternative” to SASE, as it is sometime positioned, SSE is more a step toward the ultimate goal of a SASE architecture.